Today I'm going to show you how to export your ESXi VMs via a command line tool called OVF Tool. Why is this needed I hear you ask?
This issue came about because I tried to export a VM via the ESXi 6.7 Web Admin Portal and it kept failing. I did a bit of research and discovered that VMWare had created a tool that enables you to do this via command line, so I thought I document that here.
Let's start...
First, download the OVF Tool from here...
Once you've downloaded and installed the tool relevant to your PC System Type (32bit or 64bit), we can commence the process.
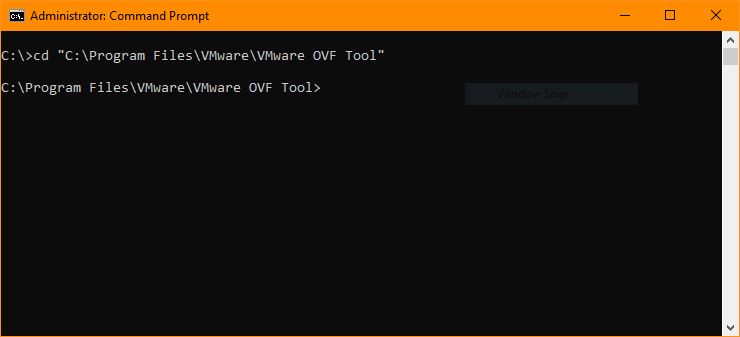
Open a command prompt as an admin and navigate to the following directory:
cd "C:\Program Files\VMware\VMware OVF Tool"
The path above represents the path that my version of the OVF Tool was installed. Yours may be different, so please change the path to suit your environment. You should have something like the following in your command prompt window:
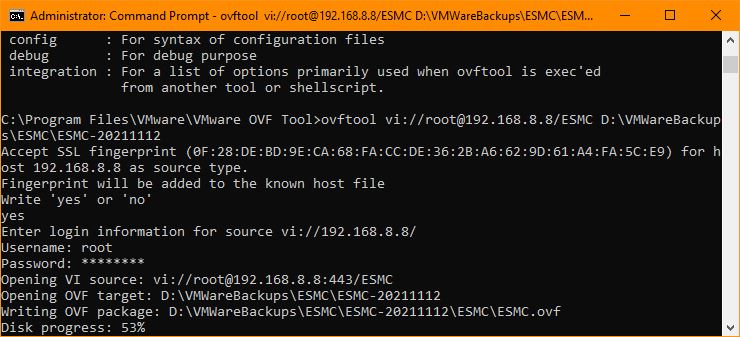
Now we're ready to export our VM to an OVF File. In my case I was exporting to an external drive and the path was D:\VMWareBackups\ESMC\ESMC-20211112. So the syntax to do that is as follows:
ovftool.exe vi://[email protected]/ESMC D:\VMWareBackups\ESMC\ESMC-20211112
So to break down what the above syntax means:
- ovftool.exe - Is the executable for the OVF Tool. This is located in the path we navigated to in the initial step of this tutorial
- vi://[email protected]/ESMC - Is the username "root" to log onto my ESXi server. 192.168.8.8 is the IP of my ESXi server and finally ESMC is the VM I want to export
Please change the values above to suit your ESXi instance. Once you hit enter you will be asked whether your want to add a fingerprint to the host file. Type "yes" and finally you'll be prompted to provide the password for your ESXi server. You will see the progress displayed of your export like in the following example:
That's it your task is complete.
If you've found this useful, you may want to sign up to our newsletter where you'll receive notices on when we post new articles and helpful "how tos". Just fill out your details below and we'll do the rest…












